Akira Ransomware
Akira is an emergent ransomware group that has been active since April 2023, targeting small to medium organizations. Here's what you need to know.
Overview
Akira is an emergent ransomware group that has been active since April 2023 (Recon InfoSec). The group has targeted small to medium sized organisations with double extortion. They have accessed environments through VPN services where users did not have multi-factor authentication enabled. The group also leverages tools including AnyDesk, WinRAR and PCHunter during intrusions in an attempt to avoid detection since these have legitimate purposes and may be common within the environment (Sophos).
The group’s name is based on the extension that is appended to encrypted files. Based on the groups listed on its victim site, the ransomware group predominantly targets North America and in particular the USA.
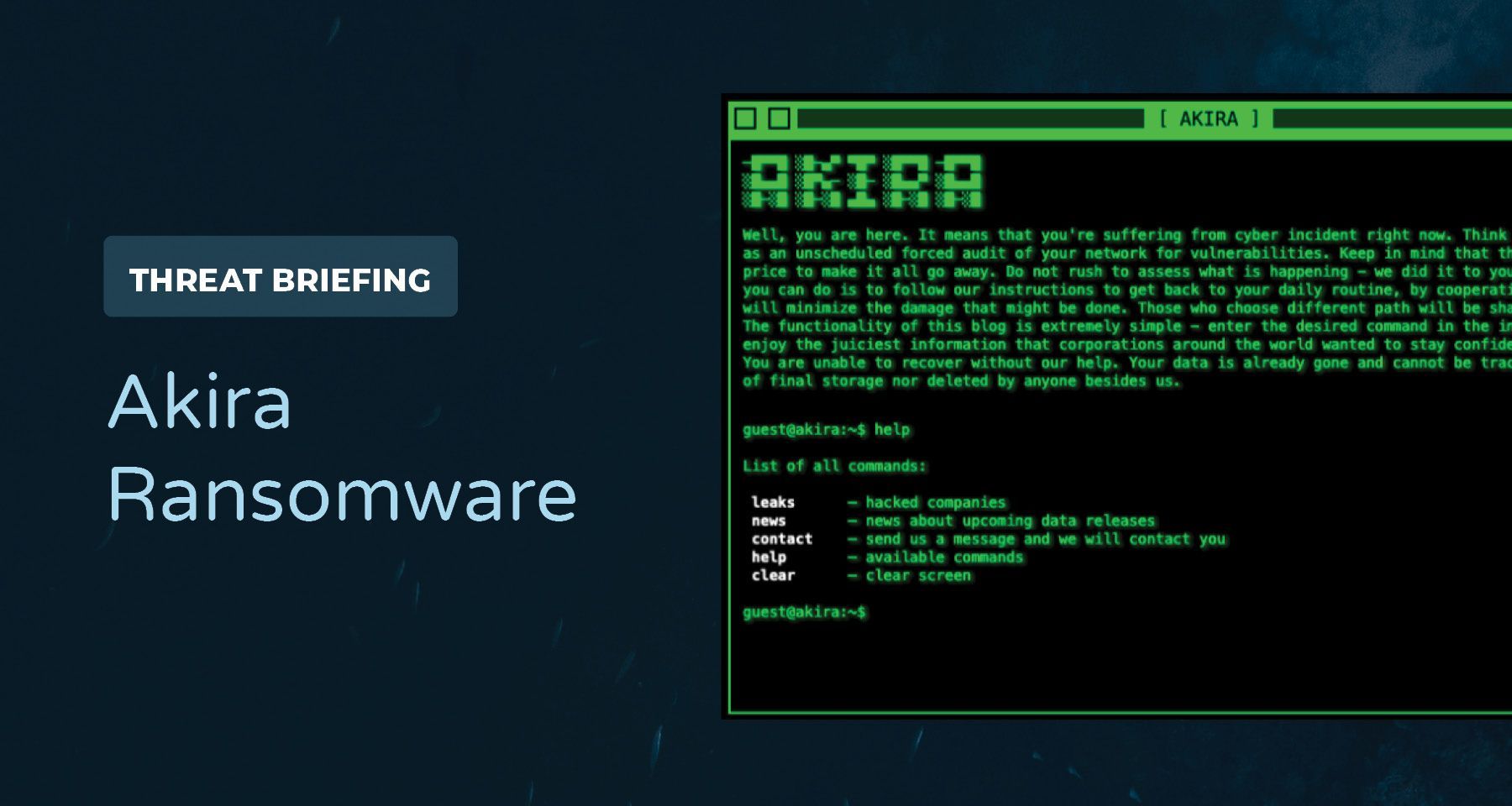
The group’s leak site supports user interaction as visitors must enter commands to access different information similar to how a terminal prompt works.
Recommendations
Based on TTPs observed during intrusions the following preventative actions can be taken:
- Ensure that MFA is enabled on user accounts
- Maintain a list of approved software that can be deployed within the corporate environment and routines search to identify unapproved software.
- Monitor for anomalous RDP traffic and restrict RDP access to user roles/groups that require it
- Monitor for changes made to backup services
Victimology
The group has been able to encrypt files in over 30 different organizations over the past few months. While a majority of victims come from the financial services sector, the group was able to successfully target a mining company that is headquartered in South Africa and claims to have targeted several businesses within the education sector including a day care group out of Toronto, Canada.
The group continues to list victims on their site in June and claims to have exfiltrated the data from at least 39 difficult organizations. 29 of the potential victims are headquartered in the USA with six operating out of Canada. The map below shows the distributions of where the claimed victims are located.
Encryption
Akira is not a destructive malware in the sense that it does not target an endpoint’s Master Boot Record (MBR) but rather targets particular file extensions. Sandbox analysis shows that when the ransomware executable runs, it calls the GetLogicalDriveStrings() API which returns all valid drives on the system. The executable will drop a ransom note that is contained within the binary as a string. The ransom note contains a link to the Akira Tor site, their negotiation site and a code used to access the negotiation channel. The note also threatens to publish data if a payment is not made.
Hi friends,
Whatever who you are and what your title is if you're reading this it means the internal infrastructure of your company is fully or partially dead, all your backups - virtual, physical - everything that we managed to reach - are completely removed. Moreover, we have taken a great amount of your corporate data prior to encryption.Well, for now let's keep all the tears and resentment to ourselves and try to build a constructive dialogue. We're fully aware of what damage we caused by locking your internal sources. At the moment, you have to know:
1. Dealing with us you will save A LOT due to we are not interested in ruining your financially. We will study in depth your finance, bank & income statements, your savings, investments etc. and present our reasonable demand to you. If you have an active cyber insurance, let us know and we will guide you how to properly use it. Also, dragging out the negotiation process will lead to failing of a deal.
2. Paying us you save your TIME, MONEY, EFFORTS and be back on track within 24 hours approximately. Our decryptor works properly on any files or systems, so you will be able to check it by requesting a test decryption service from the beginning of our conversation. If you decide to recover on your own, keep in mind that you can permanently lose access to some files or accidently corrupt them - in this case we won't be able to help.
3. The security report or the exclusive first-hand information that you will receive upon reaching an agreement is of a great value, since NO full audit of your network will show you the vulnerabilities that we've managed to detect and used in order to get into, identify backup solutions and upload your data.
4. As for your data, if we fail to agree, we will try to sell personal information/trade secrets/databases/source codes - generally speaking, everything that has a value on the darkmarket - to multiple threat actors at ones. Then all of this will be published in our blog - https://akira<redacted>.onion.
5. We're more than negotiable and will definitely find the way to settle this quickly and reach an agreement which will satisfy both of us.
If you're indeed interested in our assistance and the services we provide you can reach out to us following simple instructions:
1. Install TOR Browser to get access to our chat room - https://www.torproject.org/download/.
2. Paste this link - https://<redacted>.
3. Use this code - <redacted> - to log into our chat.
Keep in mind that the faster you will get in touch, the less damage we cause.
Figure 3: Ransom note dropped by Akira. It is dropped in a file called akira_readme.txt. This note is from a sample available on Hybrid Analysis.
The ransomware uses Microsoft native libraries to perform the encryption. This is observed as the binary calls functions from Microsoft’s CryptoAPI. One of these calls is used to import a base64 encoded public key that is hardcoded within the binary. This public key is decoded using the CryptStringtoBinaryA() which converts a formatted string to an array of bytes.
-----BEGIN PUBLIC KEY-----
MIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAylJbjtFvzHapC/sYdYK6NjxR1475Ae5BS3IZGefqC+jH2wfSZKMlKXPHxE5mS8qvx5FvJ4lj8LaN4a8V+ZrTTWoZSLTd+URHyPBVxYUyFjjaY0QPL7MIz4fH5NMo312bqjJP2MBU48AZhhGI1pNvoZT4r43077yhNe8RTIdqAugRLa9YDVbugtV4sb8mFjnxDxnDgILqtZ0QwU5/YJcTr9VZjrAnB0ltRuOygc+uj2bepBkQ0RVexAeLvMavhcfSE13YjTbBtWsDjjd++KQjdxuBbpx5Z8jOxgzbO4RxSVOgqco2PIO+r8uz+ekXVe8+Ie1ymlIk/DRkbeiRuVZaMs0Pc9BgQOI430uLmLTdZ1BXV36N8dIJnBKkyZQ6iBFbWfUOaLy5IIhW5ZRvxzto5LeJh7HKbrMDEhH2NG3+dO13tfEGWAK5d5u2P3l4TURw8mQsY5SnjIJCXEuojhlZ57+7pnZ0l7nRBJ9aL3HFZxF1EEWRVlvzotg5ncK5vGY2XoNm4mREXGF5W5szssJ2xcEtf1KazK/N5OjxZ7etXU+4RY3a0s3Kek/D+FZmfdd1N/qXctPvJSG0XRJzYvPRA4NE/mhLUebQSm2kIgXNXH/uCsdTujMyXSWqlIJxEbZJI5zsG/gevQ2F9ucyRhiPKKa6abydTBi5zM4kSntDNcUCAwEAAQ==
-----END PUBLIC KEY-----
Figure 4: Public Key hardcoded within the Akira sample on Hybrid Analysis
The binary will then iterate through files and encrypt them unless the file extension is part of the exclusion list. The following file types are excluded from the encryption process:
- .exe
- .lnk
- .dll
- .msi
- .sys
Files with these extensions are avoided in an attempt to not impact the usability of the machine. Other file types are encrypted and the files get appended with the .akira extension.
Once the files have been encrypted, the binary runs a PowerShell command to remove shadow copies through WMI. This is done to prevent restoration through a backup. Figure 7 shows the command that is executed to inhibit recovery (1490).
powershell.exe -Command "Get-WmiObject Win32_Shadowcopy | Remove-WmiObject"
Figure 7: PowerShell command used to remove shadow copies.
Example Infection Chain
Indicators of Compromise
Table 1: Indicators of Compromise identified. Source: Cyble
MITRE ATT&CK Techniques
Table 2: MITRE ATT&CK Techniques observed in Akira intrusions.
References
https://news.sophos.com/en-us/2023/05/09/akira-ransomware-is-bringin-88-back/
https://blog.reconinfosec.com/emergence-of-akira-ransomware-group
https://blog.cyble.com/2023/05/10/unraveling-akira-ransomware/


