CTI Networking Report 2024
"Sharing, Compared: A Study on the Changing Landscape of CTI Networking" is now available online.

"Sharing, Compared: A Study on the Changing Landscape of CTI Networking" is now available online. This report is published publicly and ungated. For context, an excerpt of the introduction is below.
Introduction
Cyber threat intelligence (CTI) is an evolving field, with an industry-wide consensus that teams cannot effectively operate in an intelligence silo. This sentiment is shared across all stakeholder segments – public, private, vendor, and academic. In support of improved CTI sharing, stakeholders have invested in efforts around cross-boundary collaboration, technical standardization, managing trust, and reporting best practices. However, understanding the time and effort spent in CTI networking (i.e. connecting human-to-human for improved business outcomes) is often overlooked.
In 2022, I published the inaugural study on CTI networking with a core hypothesis:
CTI networking is an afterthought in practice, in spite of its demonstrated
impact as a vital asset.
Two years later, I sought to understand what’s changed – and what hasn’t. After making a few tweaks based on feedback, I reached out directly to practitioners (again!) to capture their CTI networking experiences. While the first survey demystified how and where professionals were spending their time collaborating, this survey aimed to build on those initial findings to:
- Revisit the perceived and demonstrated value of CTI Networking
- Highlight significant changes in behaviors and attitudes
- Dive deeper into mapping how practitioners can most effectively network today, individually and within their teams
Intended Audience
- Management responsible for security program strategy to gain awareness on advantages, challenges, and best practices
- CTI practitioners looking to optimize their networking efforts and understand peer experiences
- Security and intelligence professionals in related fields seeking to expand involvement in CTI areas
- Professionals entering or pivoting into CTI careers, to demystify what it means and how to participate
Executive Summary
In the two years since the previous survey, so much has changed within the field of cybersecurity: seemingly endless vulnerabilities, high profile campaigns, threat infrastructure take-downs, and regulatory guidance/enforcement. Simultaneously, the world at large has undergone international conflict, easing pandemic restrictions, economic recession fears, social media drama, and more. In spite of these changes, our research uncovered a steadfast core of general beliefs and behaviors around CTI networking, with a few focused areas of change.

Key Findings
- Practitioners Make an Honest Effort To Get Ahead. The belief in CTI networking value remained persistent, and the reported benefits increased over the previous survey. While responses were mixed on the ease of finding and balancing efforts, consensus remained on its importance for team members at all levels and desire to find more peers.
- The Ultimate Goal Remains: Unlock 1-to-1 & P2P. Survey responses demonstrated a strong preference for 1-to-1 Direct Messaging and Peer-to-Peer Trust Groups. Data suggests that engaging in Paid Membership Groups, Industry Events, Volunteer Groups and Social Media & Public Forums were complementary in nature, helping provide highly desired access for the two highest valued, but more private methods.
- Networking Gains Visibility, But With More Restrictions. Numerous organizational challenges came to light, like issues of legal liability, a lack of formalized processes, and gaps in measuring effectiveness. In spite of these negative forces, respondents maintained their hours spent in CTI networking efforts. They even improved visibility with leadership.
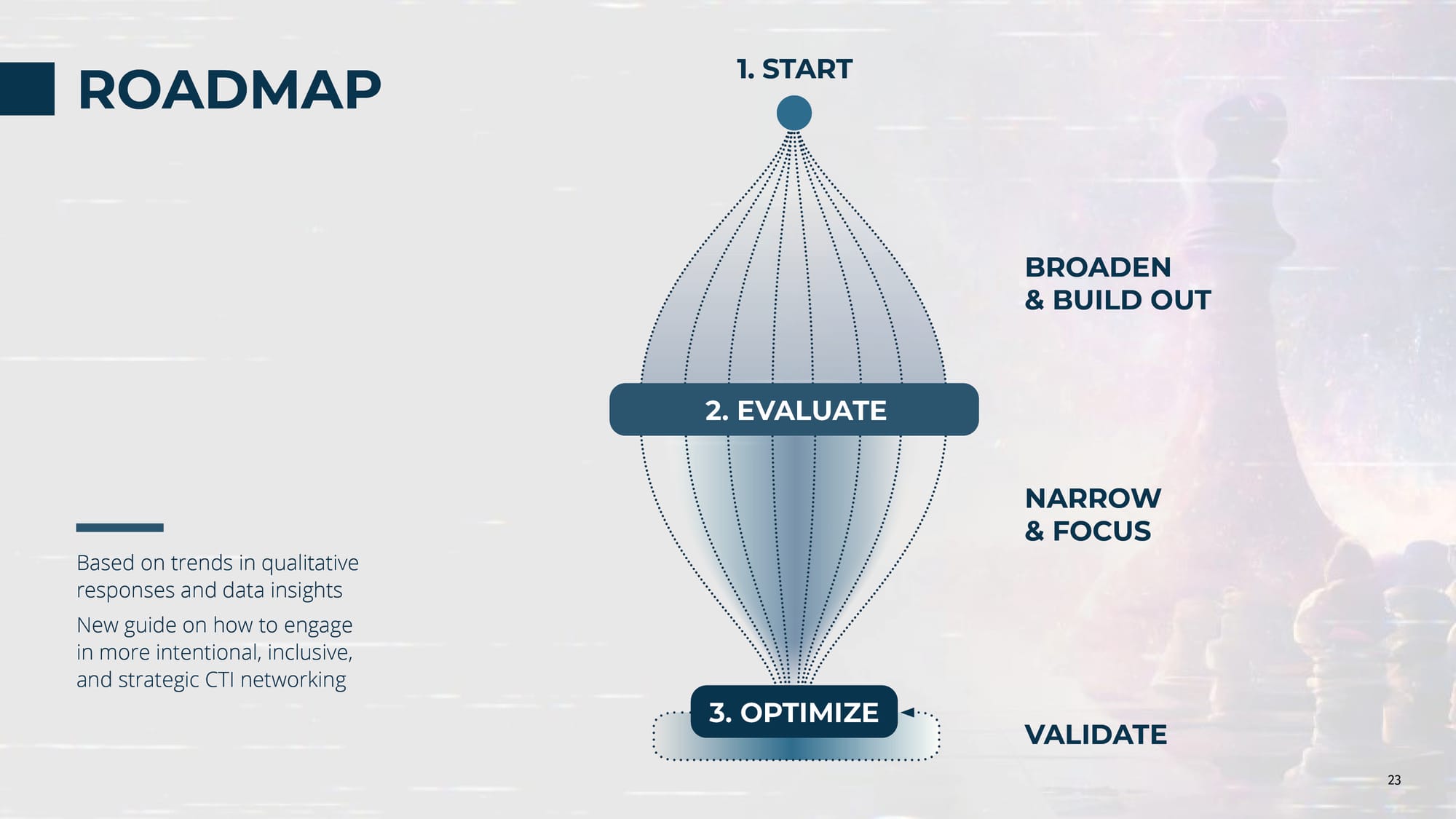
- A New Roadmap for Success: Start, Evaluate, Optimize. Based on trends in qualitative responses and data insights, a brand new guide introduces how to engage in more intentional, inclusive, and strategic CTI networking. The roadmap consists of three phases: 1) Start - Broaden and Build Out, 2) Evaluate - Narrow and Focus, and 3) Optimize - Validate.