Identifying Mystic Stealer Control Panels
Learn how to research and identify control panels for Mystic Stealer, an information stealer that appeared on underground markets in April 2023.

Towards the middle of June 2023, Zscaler and other security researchers released reports about a new information stealer called Mystic Stealer that has appeared on the underground market. According to information shared by Bleeping Computer, access to use the information stealer is being sold on a subscription basis where users can pay $150 for one month or $390 for a quarter.
This blog will go over how to identify additional control panels for Mystic Stealer. While we only look at Mystic Stealer in this case, the process can be replicated and expanded upon to find network infrastructure for different malware families. For two other excellent examples of similar investigations, check out research by @embee_research and Michael Koczwara.
Mystic Stealer Control Panel Login Page
The control panel allows operators of the information stealer to view the collected data, update settings and interact with the malware. The control panel allows operators to set the C2 IP address and port combinations that will be used by the malware and enable additional features such as anti-VM checks (Zscaler). Zscaler identified several control panels that will serve as an initial data point that we can use to find unique indicators that allow for pivoting.
Our Investigative Process
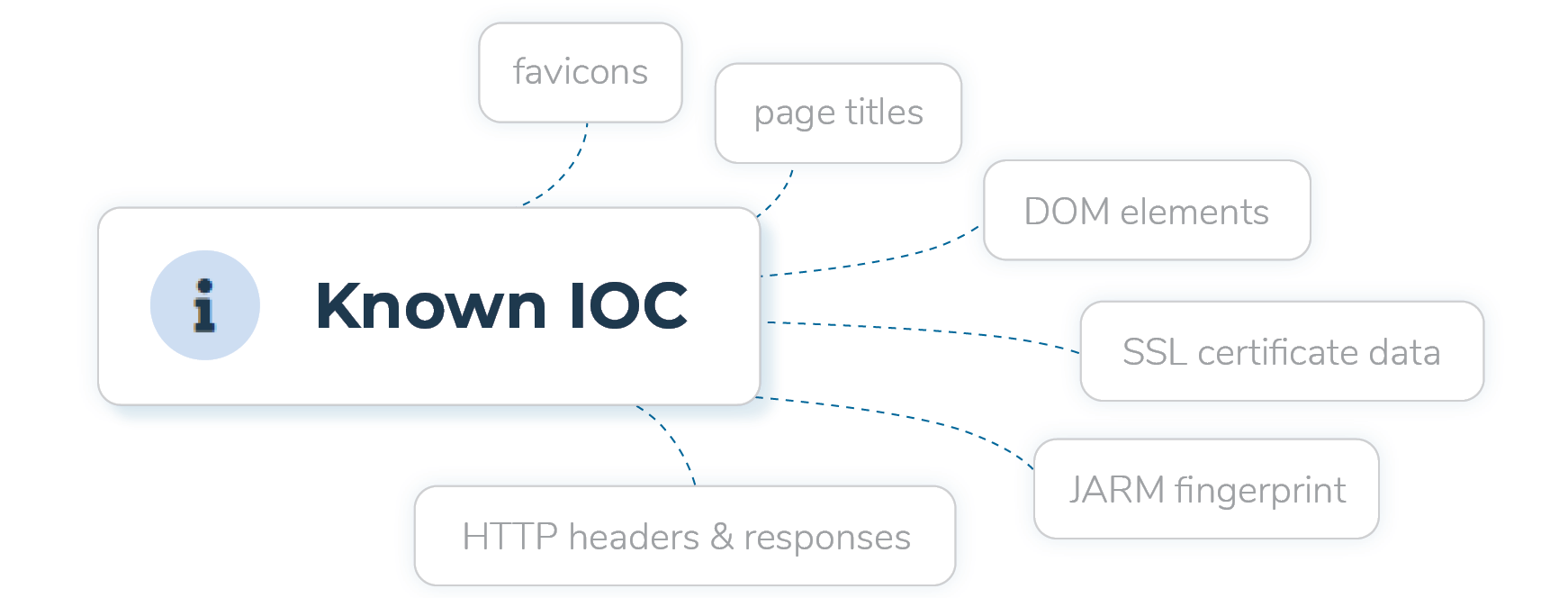
Before starting to pivot to other tools to find additional Mystic Stealer control panels, we first need to determine unique identifiers that will aid us in the investigative process. Unique identifiers are elements of the web pages or its content that are distinctly associated with the malware and not other web pages. These items can include:
- Favicons
- Page titles
- SSL certificate data such common names, or leaf certificate fingerprints
- DOM elements
- HTTP headers and responses
- JA3S hash
- JARM fingerprint
While individually each parameter might return many results or generate false positives, by leveraging multiple parameters we may be able to identify additional network infrastructure. Once we have some items to pivot from, we can query different search engines to gather additional results. The tools discussed in this blog include:
To identify parameters that can be used to pivot from, we start by looking at the Mystic Stealer control panel identified in the Zscaler blog - hxxp[://]164[.]132[.]200[.]171:8005/login/?next=/. This indicator was submitted to urlscan which we can use to review elements such as titles and DOM elements.
Switching over to the DOM representation of the web page in urlscan shows that the web page title is Mystic Stealer - Login (Figure 2). This title can be used to search other tools to find additional web pages with the same title.
Using the title identified from urlscan and switching over to Shodan, we can then identify additional results using the query http.title:”Mystic Stealer”. As of July 18th 2023 14:30 EST, this query returned 20 results. We discovered that the favicon shown in Figure 3 was a common attribute across all the results.
Binary Edge is another tool similar to Shodan, returning only 16 results as shown in the screenshot below.
Since our Shodan search revealed that all the panels have the same favicon, we can perform additional searches based on the favicon. The favicon hash is calculated and present within the raw data table in Shodan.
Twitter user @0x_99796618 was able to identify 67 panels by taking the favicon hash identified in Shodan and running the same query in FOFA according to a tweet they shared (Figure 6).
Note: some of the tools above may not provide all the details to users that do not have an account on the platform. For example, to use Shodan search filters, a user needs to be logged into the platform. Similarly, Binary edge does not allow unauthenticated search and urlscan will provide a list of similar domains only if a user is logged into the platform.
Conclusion
The process described in this blog can be used to identify additional network infrastructure associated with malware variants. In our case, we were able to determine over 30 additional control panels from the few identified in the Zscaler blog.
Each investigation is different, and there are a few pivot paths that did not yield interesting results in this specific research, but could in others. For example, the few domains that used SSL did not have any common elements in their certificates that we can use to pivot off; if there were, that would be an additional data point to aid our investigation. Michael Koczwara’s blog provides a great example of using JARM fingerprints to find additional malicious infrastructure.
The benefit of proactive searching for malicious infrastructure is that it may lead to newly setup infrastructure that can be marked as malicious and shared with the community. These shared indicators of compromise support timely detection and help responders during an investigation. For a complete list of indicators and the queries used in this blog, check out the tables below.
Indicators of Compromise
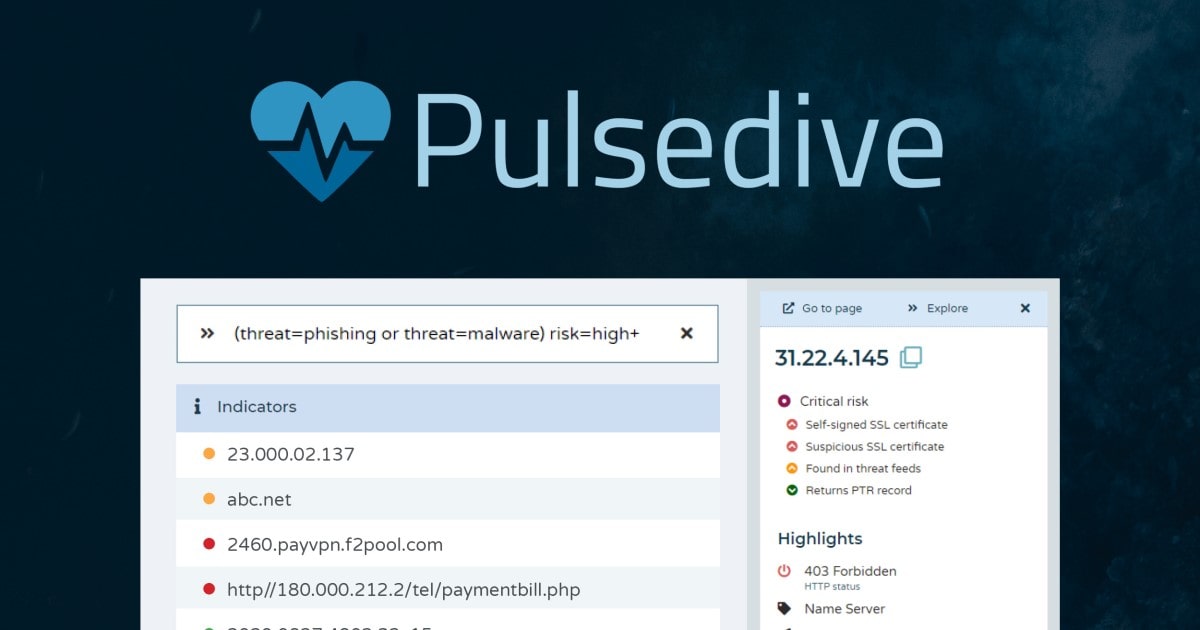
The table below contains a list of all the Mystic Stealer Console Panels that have been identified. This data can be queried in Pulsedive using the Explore query threat="Mystic Stealer". This data is available for export in multiple formats (CSV, STIX 2.1, JSON).
Queries/Search Filters Used
References
https://www.zscaler.com/blogs/security-research/mystic-stealer
https://urlscan.io/result/535841c6-ea4a-4e8c-85b7-e19bd5ad68e5#summary



